IXIA and VIAVI Solutions
Unified Performance Monitoring Solution
Combined Offering Multiplies Customer Monitoring Value
Powerful Pre-packaged Solution
The combination of Ixia intelligent network packet brokers and VIAVI Observer ensures that IT teams can optimize network performance, effectively troubleshoot applications, and investigate security issues occurring on premises or in public cloud environments. The integrated solutions provide complete access to user traffic and insight into performance, backed by full traffic capture and analysis across hybrid IT environments.

Ixia’s Dynamic Filtering for Super-Fast Filter Setup
How It Works
VIAVI and Ixia have combined forces to achieve enhanced customer value by simplifying the ordering, fulfillment, and ongoing support of pre-packaged, custom-designed Ixia network packet brokers (NPB) and CloudLens agents for public cloud visibility with VIAVI network performance monitoring and diagnostics (NPMD) solutions tailored for different common use cases. Now users can work with experts from both companies to select, configure, and deploy the optimal solution for their unique IT environment.
The combination of Ixia and VIAVI provides IT monitoring teams with a powerful, integrated solution that solves today’s challenging enterprise anomalies with:
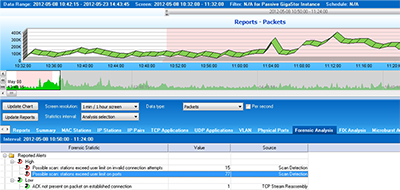
- The best long-term packet capture and post-event wire data analytics in the industry
- Outstanding visibility into all wire data sources without a single dropped packet
- No blind spot views into cloud based and virtualized east-west traffic
- Quick threat isolation to the area of interest
- Faster MTTR for critical and revenue impacting problems
About Performance Monitoring
NPBs and NPMD tools, when effectively combined multiply the gains available from each offering. NPBs excel at collating and pre-processing wire data across the entire network. NPMD tools then analyze this data for security and service level anomalies though simple workflows to resolution and high-level reporting of critical IT resources.