The network and supporting infrastructure have so much to tell you—if only you knew how to ask: What’s connected? Who is talking? What are they saying? The growing number and variety of devices and applications across today’s hybrid IT environment are becoming increasingly difficult to manage — whether related to IoT, SD-WAN, cloud migrations, or remote users at the network edge making answering these questions more urgent.
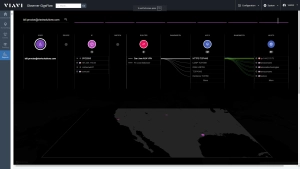
Observer GigaFlow to the rescue by integrating network, infrastructure, and user data into a single enriched-flow record captured and retained over time. Intelligently combining mountains of unstructured data into a concise record provides in-depth details on network device types, connectivity, traffic control, and usage patterns in a simple-to-understand visual. This information is maintained at the individual user/host, over time across all communication traversing the environment from any point of view making it particularly valuable for NetOps and SecOps teams when they are investigating anomalous activity.
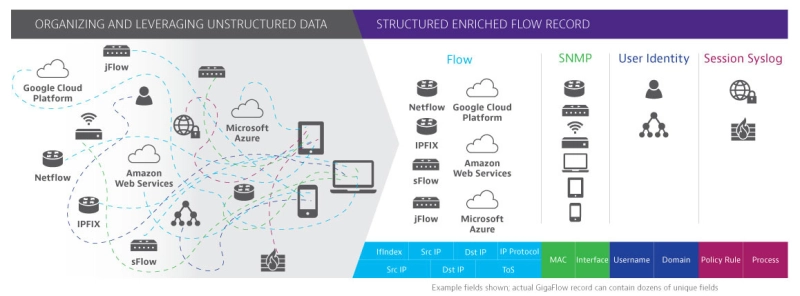
Enriched-flow data from GigaFlow now co-exists in Observer Apex with packet and metadata from GigaStor/GigaStor M. Streamlined workflows, network analysis, capacity planning intelligence, and cybersecurity investigations from a single launch point. It’s never been easier for all IT stakeholders and business leaders to have comprehensive network visibility.
Feature and Benefit Summary:
- End-user experience and infrastructure insights delivers situational awareness drives better business decisions to optimize service delivery
- High-fidelity forensic visibility into network conversations stored over time supports cybersecurity breach investigations reducing mean time to resolution
- Advanced service path visibility ensures immediate problem domain isolation across hybrid IT environments
- Cloud and virtual device insight deliver real-time understanding of performance in virtual, cloud, and remote environments
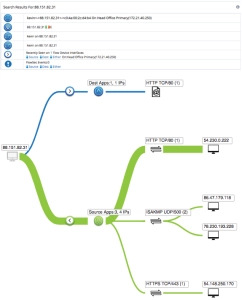
- An interactive IP Viewer that visualizes relationships between User, IP, MAC, and application usage in the network.
- Intuitive capacity planning reporting to help with proactive assessments of WAN utilization
- New workflows detailing utilization at any given site or device interface with easy drill-down into forensic-level data
-
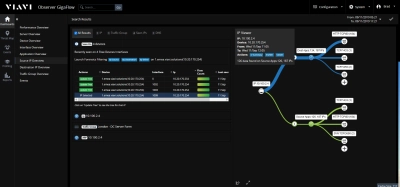
Intuitive Visualizations with IP Viewer
By compiling Layer 2 to Layer 3 insights into a single enriched flow record, Observer can produce unique, interactive visualizations that illustrate the relationships between User, IP, MAC, and application usage in the network. A NetOps or SecOps user can simply enter a name enter in a username and immediately find all devices, interfaces, and applications associated with it. Finding out what is connected and who is communicating across your network has never been easier.
-
Enriched Flow Forensics
GigaFlow offers real-time and long-term historical perspectives of end-user status and device as a function of underlying service health at every network traffic interface. The enriched flow records of GigaFlow dynamically capture all relevant data including timestamp and location continuously over extended periods. Because of this, IT teams can navigate to a specific event or anomaly in the past to troubleshoot and solve the problem by answering who it impacted and when, where, and how the incident occurred.
-
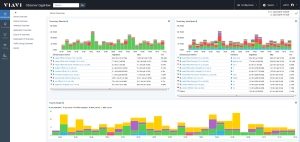
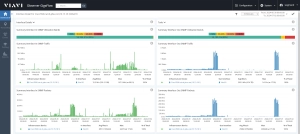
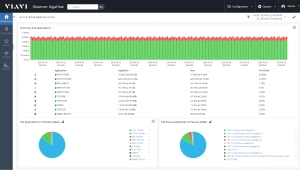
Network Capacity Planning Reports
With intuitive capacity planning reporting, GigaFlow lets IT teams conduct proactive assessments for WAN spending as well as reactive resolution of capacity-related issues. A simple, color coded dashboard highlights interfaces that are highly utilized for the most amount of time. If any congested sites are growing at any rate, more red areas will be reflected in the utilization report, suggesting that those sites may be need of upgrade. Application summary graphs can help IT teams discern which application is responsible for any growth. Drilldown into the forensic-level data is also available from the capacity planning reports.
-
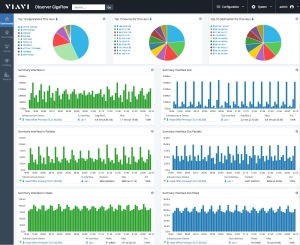
Device-Based and Site-Based Workflows
GigaFlow grants usage and utilization insights on a per interface basis down to the layer 2 switch, with graphical summaries of the busiest sites or devices and further drilldown into individual WAN links. This is ideal for general assessments of end-user experience at points anywhere along the conversation route, and valuable for quantifying asset cost/benefit efficiencies, such as when deciding where new enhancements should be made.
Designed to tightly integrate with Observer Apex, GigaFlow enriched flow records complement end-user experience scoring to accelerate troubleshooting and cybersecurity investigations.
Easy to deploy, GigaFlow clustered architecture offers carrier grade scalability and a “pay-as-you-grow” pricing model. Options are available as an appliance and in various software capacities based on number of flows supported and emitting sources to satisfy the needs of any size organization.
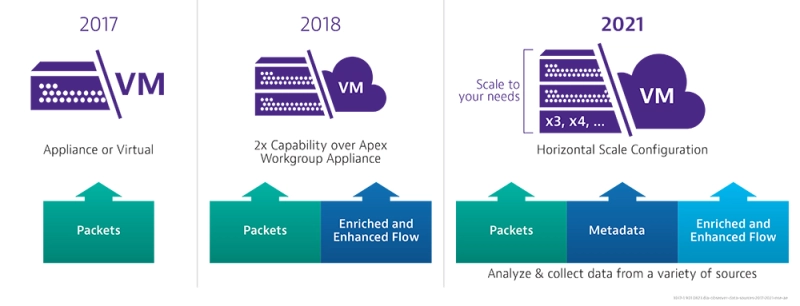
Select the GigaFlow that aligns with your IT team’s monitoring requirements.
VIAVI offers software options and an appliance to satisfy any flow per second or retention requirements. For additional information, please use the GigaFlow Calculator, or contact a VIAVI Solutions sales expert.
Literatura
Folletos
Estudios de casos
Hojas de especificaciones
Manuales y guías de usuario
Pósteres
Documentos técnicos y bibliografía
- 2024/25 State of the Network Executive Summary
- 2024/25 State of the Network Study
- Comprehensive and Actionable Enterprise Performance Management
- EMA Radar Report: Network Performance Management 2021
- From Zero-to-Insight in Three Days or Less
- How a NetOps/SecOps Alliance Can Outmaneuver the Enemy: Winning the Security Battle
- How to Optimize End-User Experience in a Cloud-Enabled Landscape
- How to Solve Six of the Biggest IT Challenges in 2021
- NetFlow vs Packet Data
- Network Observability Enables Modern Infrastructure: Capacity Planning
- Using Wire Data for Security Forensics
Descargas y actualizaciones de software
-
Observer Services
Whether it's a quick initial setup or a comprehensive on-site implementation and configuration, Observer Platform Consulting options are designed to ensure that you get the most out of your Performance Management Solutions.
Productos Relacionados
Asistencia en cada paso
Proporcionamos soporte técnico, servicios, una formación completa y los recursos que necesita. Todo ello forma parte de lo que hacemos con el fin de maximizar el valor de su inversión en VIAVI.
Déjenos ayudarle
Estamos a su disposición para ayudarle a avanzar.