Network Security Tools
VIAVI Network Security Tools provide complete threat hunting and incident response solutions.
Stop hackers with the VIAVI real-time threat hunting and security breach remediation solutions. Designed for enterprise networks, our solutions analyze traffic behavior over time and store conversations to provide a unique incident response process plan.
製品
-

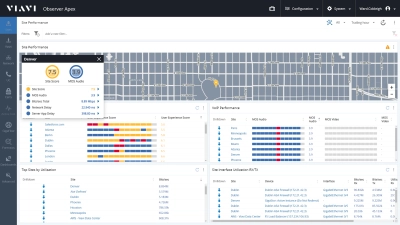
Observer Apex
Gain Comprehensive Cloud-to-On-Premises Service Visibility with End-User Experience Scoring
-

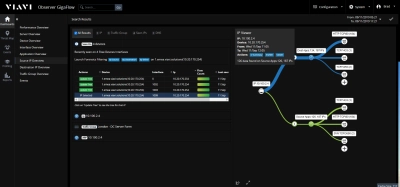
Observer GigaStor
Enable end-user experience scoring with the best packet capture, analysis, and storage solution in the industry -...
-

Observer GigaStor M
An optimized end-user experience enabling solution offering flexible deployment options for your network...
-

Observer GigaFlow
More than just flow; user, machine, network and, application data – in a single enriched record
-

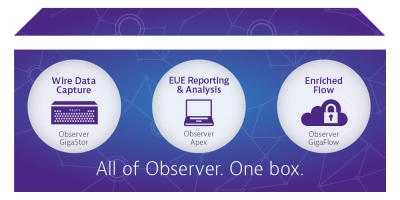
ObserverONE
Industry-leading wire data analysis without breaking the bank
-

Observer Analyzer
Observer Analyzer monitors unified communications (UC) deployments, network security performance, applications, and...
-

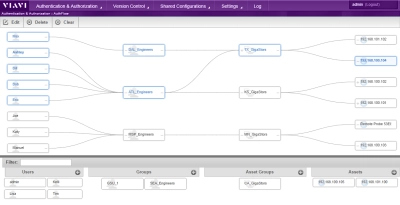
Observer Management Server (OMS)
The Observer Management Server (OMS) features simple navigation to easily control user access and password data,...
F.A.Q. about Network Cybersecurity Tools:
It is the practice of viewing, collecting, and analyzing network traffic to identify and act upon anomalies. These anomalies could potentially be Indicators of Compromise (IOCs) within your network (i.e. a breach), so it is imperative for an organization’s security tools to contain network security monitoring capabilities that can deliver close to real-time detection of potential threats.
VIAVI Observer grants NetOps and SecOps users with visibility into their network by performing both wire data and flow-based analyses on the traffic, making it a valuable addition to any organization’s network security monitoring tools.
Typically, they include a real-time threat detection system that aggregates information from multiple sources, a system to automatically alert users in case of threats, and/or behavioral analysis techniques to identify anomalies in traffic patterns and user groups that are indicative of rogue activity.
Observer offers each of these with the power of enriched flow and high-fidelity network security forensics.
In the modern world, security threats are everywhere. The repercussions for a breach are higher than ever before. In fact, the average breach costs more than $8M and the reputational damage for an organization can go far beyond. The need to invest in your cyber arsenal has never been greater.
That’s where Observer’s network security monitoring software comes in. Using advanced traffic profiling and IP blacklisting, Observer strengthens your defense by immediately identifying rogue activity and unauthorized devices. This helps with the proactive aspect of seeking out threats, but what about the reactive side?
Observer’s wire-data capture, backed by full fidelity forensics, gives security and network teams near complete visibility into the network, and this wire data is critical. In fact, according to a recent EMA study, enterprises who used wire data as a part of their normal cybersecurity toolset had shorter breach detection and response times and more confidence in workflows and processes. This means higher satisfaction from operations teams, and more time available to focus on driving optimal service delivery.
It is more important than ever for an organization to listen to their network.
According to a study conducted by the Enterprise Strategy Group, 91% of IT professionals surveyed agree that visibility into endpoints, servers, and other parts of the network enhances security monitoring practices. This illustrates the need to compile data from many types of network infrastructure sources. Only in doing so can an organization hope to adequately depict a true “beginning-to-end” view of a breach as the potential attacker traverses the network, and this view is critical to security investigations.
Indeed, attacks can come from the most innocuous of devices if they go untracked and are unauthorized. By listening to your infrastructure devices, Observer goes beyond traditional network security tools to help you understand what’s connected in your network and who is communicating across it. With Observer, it is easy to detect rogue activity across all your devices.
As network speeds and volumes continue to scale, it’s critical that any packet broker can scale to accommodate this growth without losing any packets. With Observer, your network and security teams have access to one of the only third-party validated wire data capture tools in the market, with industry leading stream-to-disk speeds. This means giving your security and network teams access to the complete picture when performing remediations.
But Observer goes beyond simply being a packet broker. In fact, Observer even offers automated threat assessment with three critical capabilities:
- IP Blacklisting: Observer will automatically call home to obtain the latest blacklisted IPs, then checks it against all enriched-flow records over time.
- SYN Forensics: Observer can also alert on syn-only flow records, often associated with rogue activity.
- Traffic Profiling: A core feature of Observer is to use the enriched-flow records to build a traffic profile of devices on the network. Profiles are maintained in real-time with all future network generated device traffic evaluated against past behavior for unusual or anomalous activity.
With the VIAVI network security software, you can aggregate threat sources and destinations from profiled and blacklisted IPs into a real-time threat map, making it a valuable addition to your organization’s set of tools.
This integrated threat map helps you drill down into specific network monitoring use cases such as:
- What was the host or device communicating with earlier?
- Where is the rogue host/device now?
- Who was using the host/device?
- What device/interface information can we glean about the event?
In the event of a breach, it is imperative to have a record of data to aid in post-event investigations. That is where Observer’s full fidelity forensics comes in. With Observer’s full fidelity packet capture, coupled with complete enriched-flow records, we dynamically capture all relevant data including timestamp and location continuously over extended periods with over a petabyte of storage.
Because of this, IT teams can navigate to a specific event or anomaly in the past to troubleshoot and solve the problem by answering who it impacted and when, where, and how the incident occurred.
Having the ability to do this with network security tools that monitor is especially important with the emerging privacy legislation like Europe’s General Data Privacy Regulation (GDPR) and California Consumer Privacy Act. With GDPR for instance, in the event of discovery of a breach, organizations that conduct business in Europe have just 72 hours to gather all breach-related information to the relevant regulator. This can be difficult if the breach happened further back than anticipated. However, with Observer’s archiving ability and wire-data capture, your organization will be assured to have wire data, enriched-flow records, and conversation metadata to report to any regulatory authorities.
Observer re-imagines traditional flow to deliver organizations with security monitoring use cases. By intelligently stitching together multiple sources of data into an enriched-flow record, Observer delivers accessible, expandable visualizations that lets users hover and sweep into User to IP to MAC relationships, usage patterns and more.
Historically, NetFlow has been a powerful dataset to allow a security tool to collect information about the network, with things like source and destination IPs of a given packet, timestamps and more. Observer’s Enriched-Flow Records go far beyond regular NetFlow data, providing you with structured insights formed from stitching together data from multiple traffic and infrastructure sources – NetFlow, SNMP, user identity, and session syslog.
This way, a security analyst can search for a MAC Address of a device and from there find all related user IDs to that MAC Address all in one place, showcasing the power of network visibility that Observer’s flow-based analysis provides.
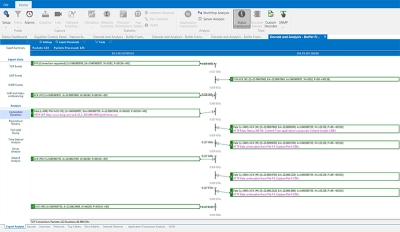
There is another aspect of network visibility that is critical to remediation – one that is the perfect complement to enriched flow— and that is wire data. Observer’s wire-data capture powered by full-fidelity forensics provide critical packet-based insights to give NetOps and SecOps the information they need after a breach has been detected. Denial of service attacks where a threat actor intentionally disrupts the service of a host connected to the network can take weeks of remediation to get it back up and running properly. With Observer’s wire-data analysis, network and security teams are empowered to quickly pinpoint where and how the data has been compromised, domain isolation of the lack of service (be it application, network, client, or server), and even an end-user experience score calculated by over 30 KPIs per socket to ensure that restoration of functionality is as quick and streamlined as possible.
One example can be illustrated in a 2019 report of a breach which compromised data related to the Mars mission in NASA’s Jet Propulsion Laboratory (JPL).
In June 2019, a malicious actor targeted an unauthorized Raspberry Pi device to access the JPL network in Pasadena, CA. This hacker went undetected for 10 months, and in the process exfiltrated approximately 500 MB of data from 23 files, 2 of which contained International Traffic in Arms Regulations information related to the Mars Science Laboratory mission.
How did this happen? Especially since the Information Technology Security Database at JPL tracks physical assets and applications on the network? Well, this Raspberry Pi didn’t have the required review and approval but was still connected.
This begs the question. How could this have been prevented? The answer can be found in Flow data. Flow-based analysis could have been used to capture information for any device connected to the network, not just a particular set of devices. But not just any flow data. Traditionally, flow is used to aggregate protocol and conversation “frequency” or “counts” but with enriched-flow records, VIAVI can help you answer what’s connected and who’s communicating in your whole network. The enriched flow of the future can stitch together information about MAC addresses, and even user ids to a given IP address.
We can break down the types of sources that feed into enriched flow into four major categories:
- Flow Sources: Routers, Switches, Load Balancers, Packet Brokers, Wireless AP’s, Firewalls, VPNs, Proxy Servers, WinFlow
- Device Sources: SNMP/ARP/CAM, SNMP/WMI, LDAP, IPAM/Asset/MDM, SD-WAN Controllers
- Cloud Sources: AWS, Azure, Google Cloud
- User Sources: Domain Servers, Authentication Servers
With enriched flow, we would have visibility into that tiny Raspberry Pi and every conversation that device is having on the network. Specifically, Observer’s enriched flow records can give you insights into the following:
- Network Device Type Information
- Interface Information
- Quality of Service Marking
- IP to MAC to User relationships
- Traffic Control Groups
- Usage Patterns
The VIAVI Professional Services ensure that you get the most out of your VIAVI network security tools. Our Professional Service Engineers serve as Subject Matter Experts in software deployment, configuration, and training.
Professional Services consists of four phases:
- Discovery: We work with you to record requirements and expectations.
- Planning: We discuss different Observer deployment prerequisites based on your network security monitoring and performance needs and draft an SOW
- Execution: We come on-site to assist with deployment and configuration
- Training: We provide custom-tailored training requirements for different network security monitoring and performance use cases as needed
We provide our customers with a Project Manager and Professional Service Engineer for each on-site visit to engage with our customer and deliver distinct client value. Together, our Professional Services teams:
- Deliver Observer network security monitoring and performance training for administrators and users
- Identify and work through new network security monitoring and performance use cases to help you get the most out of Observer
- Discuss the most important aspects of Observer and get you up-to-speed on using the product
- Collaborate with engineers across your departments for custom network security software application development
- Deliver daily updates and documents on all configuration and network security monitoring use cases discussed during training
- Provide knowledge transfer on opening a support case and accessing Observer online training.
Continue your education on information security & network security tools!
Are you ready to take the next step with one of our network tools or solutions? Complete one of the following forms to continue:
あらゆるステップでのサポート
VIAVIは、サポート、サービス、総合的なトレーニング、お客様が必要とするリソースを提供しています。これはすべて、お客様のVIAVIへの投資価値を最大化するために当社が日頃より行っていることです。
エキスパートに尋ねる
詳細、価格のお見積りについてお問い合わせください。Viaviのエキスパートがお客様のあらゆる質問にお答えします。