Análise forense e remediação de ameaças de alta fidelidade
O Observer oferece análise forense de rede abrangente de ponta a ponta para eliminar pontos cegos, minimizar o tempo de permanência e acelerar a remediação.
A alta fidelidade descreve um compromisso centenário com a reprodução detalhada que representa com precisão os dados da fonte original. Com cada nova violação de dados custando às empresas-alvo mais de US$ 4 milhões em média, chegou a hora de aplicar esse nível aprimorado de rigor à segurança de rede. A análise forense de ameaças da VIAVI aproveita o poder da captura de pacotes e registros de fluxo enriquecidos para estabelecer visibilidade de ameaças históricas e em tempo real sem precedentes.
Sua rede tem muito a lhe contar. As redes híbridas nunca foram tão complexas. A proliferação de dispositivos IoT e a adoção do 5G só aumentaram o potencial de vulnerabilidades de segurança. Firewalls, software antivírus, IDS e sistemas DLP fornecem camadas essenciais de detecção e prevenção, mas o que acontece quando os invasores inevitavelmente esquivam-se da detecção e penetram no perímetro de segurança?
O VIAVI Observer atua como uma câmera de segurança 24 horas por dia, 7 dias por semana, monitorando e analisando continuamente fontes de dados de quase todos os dispositivos e entidades de infraestrutura para avaliar o que está conectado, quem está se comunicando e o que está sendo transacionado de ponta a ponta.
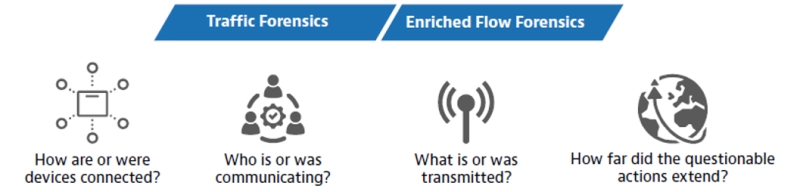
Pontos forenses problemáticos de ameaças de alta fidelidade
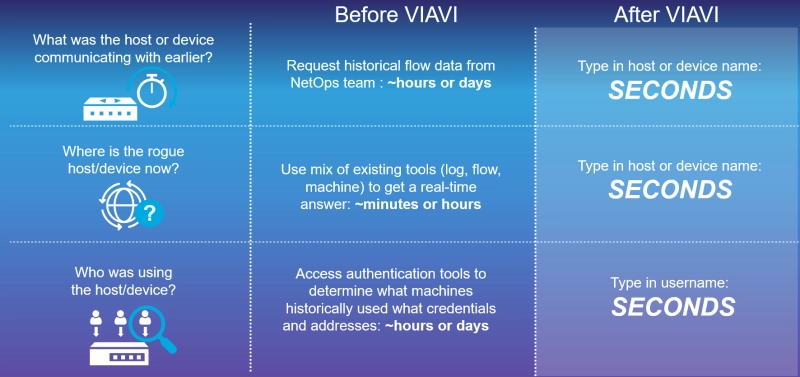
A análise forense de ameaças de alta fidelidade do Observer aborda muitos dos pontos de atenção sentidos pelas equipes de SecOps e NetOps à medida que se esforçam para melhorar a visibilidade e acelerar os tempos de resposta quando ocorrem incidentes de segurança.
- Lacunas de visibilidade:a visibilidade da rede é impedida por silos organizacionais, traduções repetidas de endereços IP e incapacidade de interpretar fontes de dados não estruturadas. As lacunas resultantes na visibilidade histórica e em tempo real exigem um modo de análise manual de “observar e comparar” que expõe dados comerciais e de clientes mais confidenciais à medida que o tempo passa.
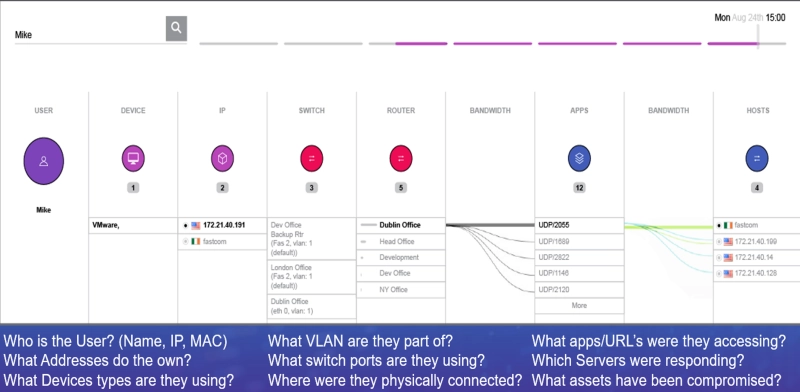
O Observer melhora a visibilidade combinando fontes de dados estruturadas com Syslog não estruturado, infraestrutura e dados do Active Directory (AD). Os registros de fluxo enriquecido resultantes ilustram claramente as relações entre o usuário, IP, MAC e uso de aplicativos na rede. - Pontos cegos da equipe de segurança:as equipes de segurança equipadas com ferramentas como IDS, IPS, firewalls e concentradores de VPN são os guardiões modernos que protegem o ponto de entrada de intrusos. Quando ocorre uma violação de segurança, eles precisam entender toda a extensão da violação, a localização do host ou dispositivo não autorizado e os ativos afetados o mais rápido possível para remediar e acabar com a ameaça. A análise forense de ameaças preenche as lacunas para minimizar pontos cegos para as equipes de NetOps e SecOps, reduzindo o tempo de permanência de horas ou dias para segundos.
Use cases
Apesar da crescente diversidade de mercados e aplicativos, todos os proprietários e usuários de redes compartilham uma participação pessoal na proteção de seus dados, aplicativos e outros ativos valiosos contra roubo ou comprometimento.
- Saúde
A proteção de informações confidenciais e a conformidade com os padrões regulatórios (HIPAA) promulgados para proteger a privacidade do paciente são de extrema importância no setor de saúde. A análise forense de ameaças de alta fidelidade agrega valor ao identificar rapidamente a origem exata e a extensão de uma violação para minimizar a exposição ao registro do paciente e determinar as ações de remediação apropriadas. - Mercado financeiro
Ativos de alto valor em dólares no setor financeiro tornam essas redes alvos primordiais para hackers, ameaças internas e fraudes. A visibilidade fornecida pela análise forense de ameaças de alta fidelidade fornece as evidências sólidas necessárias para identificar ameaças internas ou externas, ao mesmo tempo em que estabelece a granularidade de dados necessária para dar suporte a políticas de acesso de confiança zero. - Mercado de varejo
Varejistas e proprietários de comércio eletrônico lidam regularmente com grandes quantidades de dados confidenciais de clientes, POS e financeiros. As métricas aprimoradas de resposta a incidentes geradas aumentam a confiança do cliente e a resiliência a ataques futuros, ao mesmo tempo em que dão suporte à conformidade com regulamentações do mercado, incluindo GDPR e PCI-DSS. - Fabricação
Embora os dados confidenciais dos clientes tenham menos probabilidade de serem expostos em um ambiente de fabricação, essas redes devem proteger a propriedade intelectual essencial e os segredos comerciais à medida que os produtos são projetados, construídos e enviados. A análise forense de ameaças de alta fidelidade também melhora a resiliência operacional, apoiando a investigação de anomalias do sistema e da infraestrutura.
A abordagem VIAVI – valor forense incomparável
Prevenção e detecção são elementos principais da segurança de rede, mas a análise forense de ameaças traz um ingrediente intangível à mesa. Quando as ameaças inevitavelmente escapam das defesas da linha de frente, o Observer permite que você simplifique o processo de correção (e minimize o tempo de permanência) ao determinar rapidamente como os invasores entraram, quanto tempo permaneceram lá, para onde foram e o que levaram. Ao rastrear e registrar movimentos laterais, o Observer caracteriza o escopo e a gravidade da violação, fornecendo uma visão mais profunda das táticas empregadas por criminosos.
- NAT/PAT:As traduções de endereço de rede e porta (NAT/PAT) introduzem alterações em linha para endereços IP e credenciais que dificultam o rastreamento de conversas e movimentos laterais. O surgimento do trabalho remoto e da arquitetura de nuvem híbrida aumentaram esse dilema. O Observer analisa dados NAT/PAT de todos os dispositivos de tradução de endereço para construir uma visão detalhada de cada transação de ponta a ponta. As equipes de SecOps podem aproveitar esses recursos avançados para identificar a atividade de ameaças, enquanto as equipes de NetOps obtêm mais informações sobre a experiência do usuário final e a identificação do domínio do problema.
- Forense robusta:provas forenses confiáveis são caracterizadas por autenticidade, integridade e valor probatório que produzem uma fonte definitiva de verdade. Os recursos forenses de ameaças de alta fidelidade da VIAVI atendem a esse alto padrão aproveitando ao máximo os dados disponíveis de várias fontes (IPFIX/NetFlow, etc., Active Directory, Syslog, SNMP, pacotes) e estabelecendo uma pegada forense completa que não pode ser escondida por agentes mal-intencionados.
O valor VIAVI
Com cada violação de dados levando em média 277 dias para as equipes de SecOps, a visibilidade das ameaças se tornou um problema crítico a ser resolvido. A VIAVI oferece uma solução forense de alta fidelidade, robusta, compacta e escalável, com recursos e capacidades avançadas incomparáveis no mercado.
- Áreas forenses:a capacidade de armazenar registros de fluxo enriquecidos na forma de análise forense de fidelidade total combinada com os recursos de retenção de pacotes do Observer GigaStor permite que as equipes de SecOps e NetOps analisem retroativamente qualquer transação de rede e estabeleçam visibilidade de rede sem precedentes.
- Registros de fluxo enriquecido: O Observer é a única solução disponível para combinar de forma inteligente fontes de dados estruturadas e não estruturadas para criar um “super-registro” para cada conversa em toda a infraestrutura e caminho. Os registros de fluxo convencionais (não enriquecidos) são frequentemente limitados aos dados do roteador e do switch de camada 3.
- Fontes de dados integradas:dados isolados podem ser tão ineficazes quanto as operações de TI isoladas. O Observer integra perfeitamente sua análise forense de dados de fluxo e pacotes em visualizações de ação dentro do Observer APEX.
Soluções forenses de ameaças de alta fidelidade VIAVI
A plataforma Observer da VIAVI é o produto de décadas de colaboração com administradores de rede, equipes de operações e especialistas em segurança de rede. O Observer leva as práticas forenses de ameaças para o próximo nível, utilizando fluxos de trabalho predefinidos e painéis de alto nível. Os componentes da plataforma Observer modular se combinam para apoiar as metas de negócios, superando os principais desafios de visibilidade da rede, tecnologia e gerenciamento de ativos.
- Observer GigaStor: A solução de captura, análise e armazenamento de pacotes líder do mercado agora está disponível em duas versões virtuais diferentes para manter a visibilidade em todos os ambientes híbridos de TI/hospedagem em nuvem. A captura completa de pacotes e as opções somente metadados fornecem alternativas baseadas em restrições de armazenamento e custo.
- Observer GigaFlow: registros de fluxo aprimorados integram dados de rede, infraestrutura e usuário em um único registro que carrega informações detalhadas sobre aplicativos e tráfego. O GigaFlow simplifica a análise de rede, o planejamento de capacidade e as investigações de cibersegurança, fornecendo visibilidade abrangente da rede a todas as partes interessadas de TI e líderes de negócios.
- Observer Apex: A peça central da plataforma Observer também é a primeira solução de monitoramento de desempenho do mercado a gerar uma pontuação de experiência do usuário final (EUE) para cada fluxo de cliente/servidor. Painéis flexíveis suportam identificação de problemas e análise de causa raiz com base em todas as fontes de dados disponíveis para reduzir o tempo médio até a resolução (MTTR).
Artigos técnicos e livros
Data Sheets
Webconferência
Queremos ajudar
Estamos aqui para ajudar no seu futuro.
