Powering NetSecOps shared insight for fast detection, seamless collaboration, and effective resolution.
Security Operations Centers (SOCs) face an unrelenting wave of alerts, fragmented visibility, and limited context. Analysts must sift through thousands of signals to identify what truly matters, often without the packet-level evidence or service impact insight needed for confident response.
Observer Threat Forensics with threat intelligence powered by CrowdStrike® bridges this critical gap. This dedicated cybersecurity solution extends the trusted Observer platform beyond performance monitoring into advanced network-based threat detection and forensic investigation. Powered by integrated Observer Threat Intelligence, it enriches every alert with adversary context, enabling faster, more accurate, and collaborative investigation across network and security teams.
Threat Intelligence Meets Forensics
Observer Threat Forensics combines real-time threat intelligence with packet-level analysis to expose hidden risks, validate alerts with precision, and give SecOps and NetOps a unified view for faster, more confident response from a single source of truth.
Real-Time Threat Intelligence Correlation
Detect with precision.
By continuously correlating live network traffic with dynamic threat intelligence, Observer Threat Forensics quickly identifies known malicious behaviors, exploited vulnerabilities (CVEs), and attacker TTPs. Each alert is prioritized by relevance and potential impact empowering analysts to act faster and more effectively.
Forensic-Level Investigation
Validate threats with confidence.
Every alert includes a direct link to packet-level evidence, providing analysts irrefutable visibility into the event. From initial incident to lateral movement, Observer can help teams reconstruct the entire attack sequence, revealing root cause, service impact, and relevant threat intent in a single view.
Comprehensive Visibility
See everything that matters.
Full-spectrum visibility starts at the packet. By capturing and analyzing both packet and flow data, Observer delivers a complete view of every device, conversation, and communication path, helping teams uncover hidden threats, abnormal behavior, and lateral movement before they disrupt critical services.
Faster Mean Time to Respond (MTTR)
From alert to root cause in record time.
Automated correlation between packets, flows, and threat intelligence eliminates manual data stitching. When suspicious activity is detected, each alert links directly to relevant packet evidence and performance data, accelerating validation, containment, and remediation to help minimize business disruption.
Retrospective Analysis
Rewind and uncover what was missed.
Long-term metadata retention enables retrospective detection of zero-day exploits and persistent adversaries, with the solution automatically analyzing historical network activity to uncover behavior that may have evaded initial detection.
How It Works
Observer Threat Forensics correlates packet, flow, and threat intelligence to produce enriched alerts that analysts can quickly investigate and validate with forensic evidence.
Available with Observer Apex
Built into Apex, new or existing customers can activate with a subscription license. No additional hardware, software, or installation required.
Enterprise Licensing Made Simple
One subscription license covers the entire enterprise environment and applies across all deployed Observer GigaStor, GigaFlow, and Apex systems.
Continuous Threat Intelligence Updates
Observer Apex automatically downloads and refreshes threat intelligence constantly, keeping indicators of compromise (IOCs), adversary insights, and malware intelligence up to date.
-
Automated IOC Detection and Alerting
Observer Apex automatically matches indicators of compromise (IOCs) against incoming network data in real time and generates alerts when suspicious activity is detected. Alerts are triggered based on the available data sources—for example, NetFlow data supports IP-based IOC detection, while packet data enables both IP-based and Layer-7 deep inspection IOC detection.
-
Retrospective Analysis
When new indicators of compromise (IOCs) are identified, Observer Threat Forensics begins matching them against incoming network data while also analyzing previously collected data to determine whether those indicators appeared in the past. This retrospective analysis helps uncover earlier activity, including cases where adversaries used previously unknown or “Zero-Day IOCs.”
-
Threat Investigation Timeline
Observer Threat Forensics provides a session timeline that enables analysts to investigate indicators of compromise (IOCs) using time-sequenced forensic evidence. Analysts can navigate backward and forward through network activity to understand what occurred before, during, and after the IOC event, helping quickly determine whether the alert represents a real threat or a potential false positive. By presenting related sessions in context, the timeline helps analysts’ triage and investigate activity more efficiently.
-
Packet-Level Forensic Evidence
Observer Threat Forensics is supported by packet-level evidence, enabling analysts to examine the actual network activity behind alerts. By analyzing captured packets, investigators can review files transferred, web activity, and other network communications to validate suspicious behavior with greater confidence.
Downloads e atualizações de software
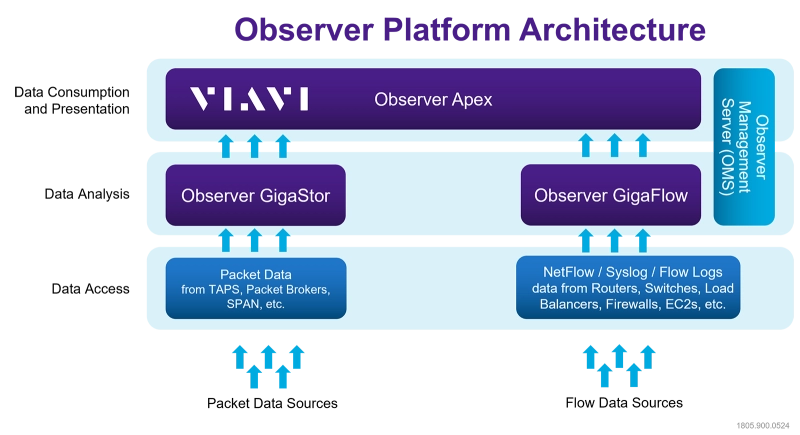
Observer Apex collects and aggregates data from Observer GigaStor, Observer GigaStor M, Observer GigaFlow to achieve enterprise-wide network observability and security visibility for NetOps and SecOps teams. By intelligently combining packet information, metadata, and enriched flow records, Apex delivers centralized management of end-user experience scoring, performance, and cybersecurity intelligence.
Add security investigation capabilities to your environment with an Observer Threat Forensics license. It extends the visibility already provided by the Observer platform by enabling IOC detection, contextual investigation, and packet-level forensic validation using the same datasets collected for network performance monitoring.
Observer Threat Forensics is available as an add-on license for Observer Apex, allowing organizations to integrate security investigations directly into their existing monitoring workflows.
Add-on Observer Threat Forensics Licensing with Threat Intelligence powered by CrowdStrike® to activate IOC detection, contextual investigation workflows, and packet-backed forensic analysis directly within the Apex interface.
Tier 1 – Apex Standard - Available as a cloud deployment (as an AWS AMI) and/or software edition.
Tier 2 – Apex Workgroup - Available as a hardware appliance, cloud deployment (as an AWS AMI) and/or software edition.
Tier 3 – Apex Enterprise - Available as hardware appliance designed for large-scale enterprise environments.
An Observer Apex deployment is required to enable Observer Threat Forensics.
Artigos técnicos e livros
Data Sheets
Folhetos
- Aumente a visibilidade no Microsoft Azure - Aproveche los registros de flujos de redes virtuales (VNet) en Observer (pt)
- Enriched Flow with Observer
- Estendendo a visibilidade do desempenho no Amazon Web Services (AWS) (pt)
- Forensics Meets Finance: A Strategic Response to EU Compliance Requirements
- Observer Apex
- Observer GigaFlow
- Pontuação da experiência do usuário final (End-User Experience, EUE) (pt)
Downloads e atualizações de software
-
Observer Services
Whether it's a quick initial setup or a comprehensive on-site implementation and configuration, Observer Platform Consulting options are designed to ensure that you get the most out of your Performance Management Solutions.
Assistência em cada passo
Oferecemos assistência, serviços, treinamento completo e os recursos de que você precisar. Isso tudo faz parte do que fazemos para maximizar o valor de seu investimento VIAVI.
Pergunte a um especialista
Fale conosco para obter mais informações ou receber uma cotação. Temos especialistas que lhe darão a resposta certa para qualquer pergunta.






