What is Packet Capture?
Learn all about packet capture and explore the tools you need to take your packet capture analysis to the next level!
In computer networking and telecommunications, transmitted information is formatted into units of data called packets. Each packet contains control information (header data) and user information known as the payload. The header is stripped away when the data reaches its destination, and the payload data is reassembled into the intended format. As the building blocks of online communication, packets are also a valuable source of information and insight into network activities.

Packet capture and analysis allows IT teams, network administrators, and security teams to continuously record what has happened on the network. Analyzing this data with advanced packet capture tools quickly leads to actionable information while making it easier to get to the root cause of performance and security issues.
Is relying on Meta-Data only good enough? Metadata, or “data about data” conserves storage space while providing a useful summary of more detailed data. Metadata is sufficient for many monitoring applications, but only complete packets contain the deep source of forensic data needed to solve complex security and performance problems. Realizing the importance of packet data inside and outside the cloud, many AWS, Azure, and Google customers are leveraging remote packet capture to bolster their security and compliance.
Is relying on Flow data (NetFlow, IPFIX, etc) only good enough? Flow data and the metadata derived from it play a crucial role in network troubleshooting. Because the customer’s existing network elements build and then send flow records to flow collection devices, it is not necessary to further instrument a network with additional monitoring points.
Flow data will summarize network conversations at a high level (who is talking to whom, which protocol(s), how much data, and QoS markings). However, packet analysis and packet metadata are required to understand KPI’s like response time, retransmissions, and the actual payloads transmitted.
Packet inspection, filtering, and encryption processes are essential for maintaining network security. Packet capture takes network security and forensic analysis to the next level by utilizing packets as the single source of truth. Packet capture also supports compliance activities by ensuring network traffic is monitored and anomalies can be detected and resolved reliably.
- What role does flow play in security?
Flow data rooted in the NetFlow protocol plays a strong role in security by capturing IP address, protocol, and port information that identifies what devices are connected, who’s connected, and what they are saying. The enriched flow records produced by VIAVI Observer GigaFlow add syslog, firewall, and VPC flow log data to the mix while mapping usernames to IP addresses. Flow data leaves behind a detailed record of everything a bad actor or exfiltration campaign tries to touch, and when. - How does VIAVI utilize both packets and flow?
To use an analogy, flow data is like an alarm light indicating a problem, while packet data is like the surveillance video and fingerprints used to prosecute a crime. While flow data provides a useful record of who or what was communicating on the network, only full packet capture solutions provide details on what the bad actor has stolen. The combination of both data sources forms a complete picture that eliminates security blind spots, makes it easier to spot indicators of compromise (IOC), and accelerates remediation after a breach. - The VIAVI role in Zero-Trust
Zero-trust is based on an assumption that no one (including machines) requesting access to systems or applications should be trusted immediately. Everyone must prove their identity and explain why they need access. This extreme security practice creates a fence with a high barrier to entry. VIAVI packet capture tools validate zero-trust solutions by tracking exactly what users are accessing and identifying holes in the zero-trust perimeter. - Packets as the ultimate source of truth
Calling packets the “ultimate source of truth” might sound overly ambitious, since they are just one element of a complete cybersecurity solution. What sets packets apart from flow data and other information captured through monitoring is the completeness of the record. Full packet capture provides a complete back-in-time resource that can recreate any network event in detail. A packet capture appliance can also reveal exactly what was taken during a data breach. - How do packets help to ensure compliance?
Since packet capture is so useful for digital forensics, it is also extremely valuable for compliance reporting and regulatory investigations. Finance, legal, and healthcare industries require back-in-time review and analysis capabilities to support data protection and privacy policies. For the telecommunications and cloud computing industries, packets verify adherence to specific SLAs. The scalable VIAVI Observer platform allows you to capture and store unlimited flow and packet data for as long as necessary.
The benefits of network packet capture extend far beyond security and compliance by providing a valuable resource for monitoring and improving network performance.
- The importance of performance
Because today’s networks are so fast doesn’t that compensate for most network issues where network bandwidth was the limiting performance factor? Ironically, today’s blazing network speeds have only raised the bar for performance, making users even more sensitive to delays. Network monitoring practices like packet capture do not impact latency, but protect online presence by preventing serious and intolerable delay, jitter, or downtime. Packet capture also provides an ultimate source of network performance truth, diagnosing a “slow network” down to the specific server, application, or network link. - How packets help determine the scope and impact of network changes
When a network change, upgrade, or reconfiguration is completed, how can you tell if service performance is improving or degrading? By capturing and analyzing packets before and after the change, network administrators can determine whether key performance indicators like response times, throughput, and latency have improved. They can also identify any new bottlenecks that were caused by the change. - How does packet capture aid in looking at performance issues?
Packets and packet capture software provide complete insight into what transpired on the wire. Response times, retransmissions, and hundreds of other metrics and calculations paint a complete picture of the user experience. With this comprehensive data, it is easier to diagnose which factors impacted performance, and which did not.
By putting over 20 years of packet capture and analysis experience to work, VIAVI has established solutions that seamlessly convert network data into expert performance insights. This new standard replaces complex three-pane decodes that present packet lists, payload data, and HTTP packet capture data separately. - Packets, end-user experience, and domain isolation
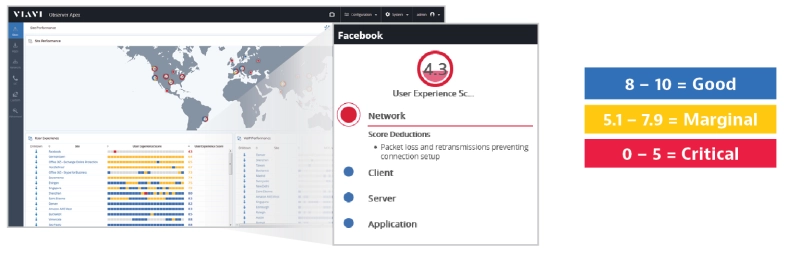
Can you truly understand the end-user's experience based on just packets? End-user experience monitoring prioritizes network data sources based on the quality of experience delivered to users. The patented End-User Experience Score from VIAVI uses machine learning to interpret multiple KPI’s and presents the end-user's experience on a scale of 1-10. Additionally, within the score we provide the health of the four main problem domains (application, server, network, and client) for fast problem domain isolation. Domain isolation accelerates mean time to resolution (MTTR) and mean time to innocence (MTTI) to determine which team or organization should own the problem.
What is a Packet Analyzer?
A packet analyzer is a network monitoring tool used to capture and examine traffic moving in and out of the network. The analyzer interprets packet header and payload information based on the protocol in use. A packet analyzer also generates actionable insight and information gained through the packet capture process.
- How a packet analyzer is used. Once the packet capture appliance and software have been installed and monitoring points are identified, the packet analyzer can be configured for its intended use. Filtering settings allow you to capture 100% of the packets or only specific packet types:
- ARP packet capture is used to support the mapping of IP addresses to MAC addresses.
- VXLAN packet capture is used to monitor and analyze encapsulated Layer 2 traffic over Layer 3 networks.
- The best packet capture appliances can be set for 24/7, 100% duty cycle capture to support unlimited back-in-time analysis.
- What is TCPdump used for? Originally written in 1988, TCPdump is a packet analyzer program used for packet capture, network monitoring, and troubleshooting. TCPdump works with Unix-like operating systems, allowing users to capture and display TCP/IP and other packets transmitted over a network interface. TCPdump is among the packet capture applications most often used by network administrators, software developers, and security teams.
Packet Capture Tools
The VIAVI Observer Platform is the culmination decades of collaboration with network administrators, operations teams, and network security experts. Efficient workflows and intuitive dashboards take packet capture analysis to the next level.
- Observer GigaStor: The industry-leading packet capture, analysis, and storage solution empowers IT teams with in-depth network conversation details for troubleshooting, performance optimization, and security investigations. GigaStor is also available as a virtual appliance while providing options for full packet capture or metadata-only.
- Observer GigaFlow: Only the combination of flow data and packet capture and analysis can provide the 360° visibility needed to assess network performance and security from all angles and eliminate blind spots. GigaFlow delivers enriched flow records that integrate user, network, and infrastructure data into a single record.
- Observer APEX: The centerpiece of the Observer platform is also the industry’s first performance monitoring solution to generate an EUE score for every transaction. Backed by the power of packet capture, the intuitive Observer Apex interface provides a window into the duration, scope, severity, and root cause of network issues.