TeraVM は、アプリケーションおよびセキュリティパフォーマンスの検証ソリューションで、ネットワーク機能とサービス展開の両方の機能テストとパフォーマンステストに使用され、さまざまなネットワークおよびセキュリティデバイスをカバーし、以下の評価に包括的なカバレッジを提供します。
- 脆弱性の露出:TeraVM サイバーセキュリティ脅威データベースにより、ユーザーは最新のサイバーセキュリティ脅威によるセキュリティの境界のパフォーマンスを評価できます。
- アクセス/認証/認可:TeraVM は、サードパーティ VPN クライアント、シングルサインオン(SAML)、および端末リモートアクセス接続(EAP-MD5)を幅広くサポートします。
- ポリシー管理:TeraVM の端末とアプリケーションのフローごとのエミュレーションにより、BYOD およびブラックリストに登録された URL/DNS を含む、いくつかのポリシー管理ソリューションの検証が可能になります。
実際の VPN クライアントでテストする
TeraVM は、アプリケーションを備えた Cisco AnyConnect SSL VPN クライアント、アプリケーションを備えた Cisco AnyConnect IPsec VPN クライアントなどの VPN ベースのユーザーを含む、ネットワーク上の多数の個別ユーザーとして機能するように使用することができます。これは VPN トラフィックの「シミュレーション」ではなく、TeraVM が実際のリモートワーカーとして機能し、Cisco FTD/ASA 上で多数の個別の有効な接続を確立し、アプリケーションフローを送受信します。TeraVM は、VPN とアプリケーションの両方のパフォーマンスをリアルタイムで測定します。TeraVM はまた、他の VPN クライアントを大規模にエミュレートして測定します。
ターゲットデバイステスト - VIAVI は、セキュアな VPN アプライアンス、エンタープライズコール管理デバイス、ファイアウォール、IMS セッションボーダーコントローラー、およびレイヤー 4~7 アプリケーションのスケーラビリティのパフォーマンスのテストに広く使用されています。当社の VPN クライアントエミュレーションのユースケースの詳細をご覧ください。
脅威分析によるリスクの最小化
ほぼ毎日セキュリティ侵害が報告され、多くの企業が組織の IT システムに対する攻撃未遂の検出を報告していることから、潜在的なセキュリティ上の脆弱性の場所を特定することがこれほどまで重要になったことはありません。
セキュリティと攻撃の種類は、ボット攻撃から従業員の認証情報の窃盗、ネットワーク上でのなりすましに至るまで、さまざまな形態をとります。
今日の多くのオンラインレポートでは、通常、次のような形で侵害が強調されています。
- ウイルス、スパイウェア、またはマルウェア: その結果、金銭や知的財産の損失につながります
- 脆弱な、または存在しないセキュリティアクセスポリシー:内部的に弱い BYOD ポリシー、外部の実装が不十分な認証サービス
- なりすまし: フィッシングメールまたは詐欺的なオンラインウェブサイトへのアクセスによる
- TeraVM を使った未知の脅威に対するセキュリティ保護、脆弱性を発見
潜在的な脆弱性が存在する場所を知ることは、より優れた堅牢なセキュリティを実現するための鍵となります。多くの人にとっての課題は、安全なアクセステクノロジー、BYOD デバイスポリシーの信頼性を検証し、セキュリティの境界のパフォーマンスを継続的に監視する必要があることです。
当社のサイバーセキュリティ脅威分析のユースケースの詳細を読む
ポスト量子暗号
ポスト量子暗号(PQC)プロトコルの実装は、ネットワークパフォーマンスオーバーヘッドを増大させ、エンドユーザのエクスペリエンスに影響します。PQC ベースのものを含め、暗号システムの開発と展開にはテストが不可欠です。ポスト量子暗号は、量子コンピュータの脅威に対して安全なアルゴリズムを作成することを目的としています。テストは、ポスト量子暗号のいくつかの主要な分野を支援します。
- セキュリティ保証
アルゴリズム耐性テストは、PQC アルゴリズムの暗号攻撃に対する耐性を検証します。これには、復元力を評価するために、古典的アルゴリズムや量子アルゴリズムを利用したものを含め、さまざまなシナリオの下でのアルゴリズムが含まれます。 - 性能評価
計算効率:テストは PQC アルゴリズムの計算効率を評価します。これには、暗号化/復号化速度、鍵生成速度、システム全体のパフォーマンスの測定が含まれます。PQC アルゴリズムの効率を確保することは、実用的なアプリケーションに広く採用されるために極めて重要です。 - 相互運用性テスト
既存システムとの統合 暗号システムは、多くの場合、確立されているインフラやプロトコルとの相互運用を必要とします。PQC アルゴリズムを多様なシステムにシームレスに統合し、互換性の問題を回避することを保証するためには、テストが不可欠です。 - 標準化コンプライアンス
標準への準拠:テストにより、PQC アルゴリズムが確立された暗号標準に準拠していることが確認され、プラットフォーム間の相互運用性と実装の一貫性が促進されます。
SASE テスト
セキュアアクセスサービスエッジ(SASE)は、従業員がどこからでも企業の機能やデータに安全かつ効率的にアクセスできる新しい方法です。
クラウド展開されたアプリケーションとデータの出現と、多様な作業場所が組み合わされたことにより、この変化が加速しました。
IT 組織は、企業データとセキュリティが侵害されないようにすると同時に、レイテンシ、スループット、応答時間の劣化によって生産性が妨げられないようにしながら、従業員に高速で安全なアクセスを提供するという難題に直面しています。
SASE はソリューションですが、企業が直面しているサービス展開上の課題は数多くあります。
- SASE とプライベートアプリケーション間の VPN リンクの容量はどれだけですか?
- SASE ソリューションは認証済みおよび未認証のウェブアプリケーショントラフィックをどれくらい処理できますか?
- エンドユーザーのパフォーマンスは負荷条件が異なると変化しますか?
- いくつの接続を維持できますか?
- トンネル内でどれだけのトラフィックを伝送できますか?
- 冗長性は必要な場合に機能しますか?
- すべてが、分散型マルチクラウドプラットフォーム全体でシームレスに機能しますか?
- Teams によるコラボレーション、VoIP、メディアストリーミング、ビデオ会議などのレイテンシの影響を受けやすいアプリケーションは、サービスに影響を及ぼす問題なしにオンデマンドで動作しますか?
- データスクラブ中にサイバー攻撃を受けるとパフォーマンスが損なわれますか?
SASE を安全に展開するための最も迅速かつ安全な方法は、ラボで精力的にテストすることです。
TeraVM SASE テストを使用すると、企業の従業員はラップトップを使用していつでもどこでも安全な接続、運用効率、24 時間無休のアクセスを確実に得ることができます。
-
セキュリティと復元力
TeraVM は、スケーラブルな現実世界のアプリケーションと脅威エミュレーション機能を提供します。このエミュレーションでは、一般的なCVE(Common Vulnerability and Exposures)リポジトリにある本当のインターネット脅威が利用されます。頻繁なアップデートにより、ユーザーはアプリケーション、攻撃、標準の継続的な変化の中で、セキュリティ態勢を評価することができます。詳細を見る
-
セキュアなアクセスとアプリケーションの完全性
TeraVM は、クライアントレス(SSL/TLS/DTLS)とクライアント(IPsec IKEv1/v2)指向の VPN の両方に対応し、多くの認証、完全性、暗号アルゴリズムを使用してパフォーマンスを検証します。さらに TeraVM は、セキュアなトンネルを通過するユーザーアプリケーショントラフィックのパフォーマンスを検証し、ポリシー設定への実際的なアプローチを実現できます。
-
NFV への確実な移行
TeraVM の NFV テストソリューションを使用すると、仮想化されたネットワーク機能のパフォーマンス、信頼性、予測可能性を確保できます。TeraVM は、通常の VNF として NFV システムにオーケストレーションできる唯一のテストソリューションであり、Traffic as a Service を可能にすることで、高信頼の次世代ネットワークサービスを提供できるようにします。詳細を見る
-
ブログ-
Navigating the Post-Quantum Future: Insights from ETSI’s Quantum Safe Cryptography Conference and VIAVI’s Role in Performance Testing
-
ニュースリリース-
MWC Barcelona 2025: VIAVI Showcases Solutions to Optimize and Secure Networks Over the Air, Through the Cloud and Into Space
-
ニュースリリース-
VIAVI、ポスト量子暗号展開のための性能試験を発表
-
ニュースリリース-
VIAVI が 2023 年秋の O-RAN プラグフェストで 8 か国にわたるベンチマークと検証を提供
ビデオ
- 5G Core Security Test
- Open RAN End to End Automated Testing Demo
- RIC Energy Saving
- Security Access Service Edge (SASE) Test
- Talking O-RAN with Sameh Yamany, CTO
- TeraVM - Testing without Limits
- TeraVM 5G Core: AMF Wraparound Test
- TeraVM Emulates 20,000 VPN Client
- TeraVM F1 Load Generator and O-DU Simulator
- TeraVM O-CU Tester and O-DU Simulator
- TeraVM SA 200 Gbps Throughput
- TeraVM: Cybersecurity Database UI
- TeraVM: Dynamic Goal Seeking Controller
- TeraVM: Enabling validation for NFV Labs with Open Source MANO
- TeraVM: Northbound API testing in OpenStack
- TeraVM: Simplifying Performance Validation for Security
- TeraVM: SMF Bracket Test for 5G
- TeraVM: UPF Wraparound Test for 5G
- Testing 5G NTN in the Lab
- VIAVI 5G Solutions Overview
- VIAVI Dell MWC 2023
- VPN Management Solution
- World's First TeraVM O-RAN O-CU Test Running on AWS Outposts
- x-App Training Traffic Steering Demo
ウェビナー
- How do you test 5G Non-Terrestrial Networks prior to space launch?
- Network Slicing – Test Now, Succeed Later
- O-RAN Testing
- RAN Intelligent Controller, the heart of O-RAN
- Security Test Considerations for 5G PART 1
- Security Test Considerations for 5G PART 2
- The Sudden Rise of Open RAN
- Understanding 5G: Lessons from the Field
Webinar Series
アプリケーションノート
- Deploying TeraVM in an OpenStack Environment
- O-RAN 仕様のテスト一式 (日本語)
- Palo Alto GlobalProtect VPN Emulation on TeraVM
- Salt Typhoon Test Lab
- TeraVM Feature Guide - Network validation for the Internet of Things (IoT)
- TeraVM-vRAN: Cellular IoT Module
- TeraVM: Network Performance Testing for VoIP
- TeraVM: Next Generation Firewall Validation
- VXLAN Testing with TeraVM
- 通信の未来に備える: 量子安全技術の台頭 (日本語)
ケーススタディ
ソフトウェアおよびファームウェアのリリース
データシート
- AWS Platform Support for TeraVM
- Google Platform Support for TeraVM
- Microsoft Azure Platform Support for TeraVM
- NetSecOPEN on TeraVM
- TeraVM 5G Core AMF Wraparound Test
- TeraVM 5G Core Security Test
- TeraVM 5G SA Core Test for TVM-vRAN SMF Wraparound Test
- TeraVM 5G SA Core Test for TVM-vRAN UPF Wraparound Test
- TeraVM at Cisco
- TeraVM Overview: What is TeraVM?
- TeraVM Specifications
- TeraVM: Oracle Cloud Platform Support
パンフレット
- Accelerate Advanced 5G and 6G Research and Development Projects
- Containerized TeraVM Security Test Solution
- NITRO Wireless Post Quantum Cryptography (PQC) Test
- SASE Test
- TeraVM Ethernet over GRE (EoGRE) Validation for WiFi-offload
- TeraVM Integration with QualiSystems CloudShell
- TeraVM Voice, Video and MPEG Transport Stream Quality Metrics
- TeraVM: Cybersecurity Database
- TeraVM: IMS Messaging
- TeraVM: Security Assertion Markup Language (SAML)
- TeraVM: Teraflow
- TeraVM: Testing LTE/4G Evolved Packet Cores
- TeraVM: Testing Multicast Based Video Services with TeraVM
- Testing Telepresence with TeraVM
ホワイトペーパーおよび書籍
- Can we conquer the challenges of open RAN rollout?
- Dimensioning Enterprise Cloud Platforms for Bring Your Own Devices (BYOD)
- FV Enabling Automation and Performance Validation for Network Services and Labs
- NFV Enabling Automation and Performance Validation for Network Services and Labs
- NITRO Wireless Open RAN Test Suite 2024
- O-RAN: 5G アプリケーション を支えるオープンなエコシステム (日本語)
- Performance Testing for Multicast Services Using TeraVM
- SASE Test Explained
- TeraVM Accreditation report for NetSecOpen Test Methodology
- Testing, Measuring and Managing PQC Migration
- Voice Analysis for Mobile Networks
- VPN Performance Validation
-
Repair and Calibration
Our products live in rugged environments for more than 10 years with 1000s of test connect/disconnect cycles. We will be there to support you to ensure components that require maintenance like connectors, batteries, and software updates are ready to test accurately for years to come. We apply factory procedures fast, automated calibration and functional verification, maintenance using OEM parts, and the application of all engineering change orders and software updates. Services are available through contract Care plans, FleetCare or per incident as requested.
Top 4 Reasons to Choose VIAVI for Your Repair and Calibration Needs:
- Minimize business disruption
- Budget
- Measurement Accuracy and Product Reliability
- Measurement Compliance, TL9000 certification and OEM Standards
-
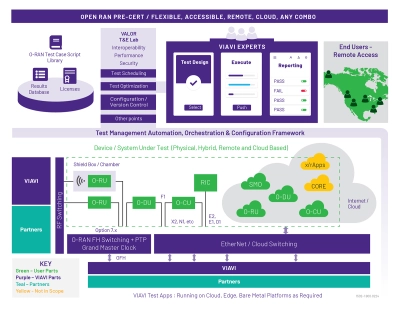
VIAVI Automated Lab-as-a-Service for Open RAN (VALOR)
VIAVI Automated Lab-as-a-Service for Open RAN (VALOR) is a hybrid Lab-as-a-Service and Test-as-a-Service lab based on VIAVI’s industry leading NITRO® Wireless test portfolio. This solution is designed to manage and support 5G and Open RAN projects that would benefit from access to tools and expert staff with a minimal ramp-up time.